Why the fuck did I write a Rust crate?
tl;dr summary
I wrote a Rust crate for Freebox OS because vulnerability research stopped being fun once curl and Python scripts became the weakest part of the investigation. The crate turned auth, tokens, TLS, typed endpoints, and raw probing into reliable primitives while I reported two vulnerabilities, kept digging into a third, and accidentally rediscovered an old Freebox easter egg.
table of contents
This started with a challenge: could I get something RCE-shaped on a Freebox, software-only?
I had been reading hardware-heavy research like Lennert Wouters’ Starlink terminal work: WIRED, Ars Technica, and Glitched on Earth by Humans. The work is sick. The hardware part is less sick when you are bad at hardware.
So I looked at my Freebox instead.
The first tooling was curl, Python, requests, JSON, and regret. That worked for a first look, then immediately became annoying. Freebox OS has auth, sessions, physical app approval, tokens, TLS quirks, and a large REST-ish API surface: system config, LAN, DHCP, downloads, filesystem, Wi-Fi, TV/PVR, storage, firewall, VMs, domotics, and more.
Every probe needed the same ceremony before the interesting request could even happen.
So I wrote freebox-rs.
Why Rust?
Because I wanted to learn Rust.
Also because the problem fit Rust nicely: typed auth, token storage, async HTTP, redacted secrets, builders, TLS policy, typed endpoints, and raw escape hatches for the weird parts.
The API became boring in a useful way:
let client = Freebox::client_for(&base_url, TlsPolicy::Auto)?;
let token_store = TokenStore::default_for(&app)?;
let freebox = Freebox::from_app_token(client, base_url, app.app_id, token.app_token);
let config = freebox.system().config().await?;No exploit magic. Just the annoying part made reliable.
What it enabled
The crate made ideas cheap.
I could authenticate cleanly, enumerate domains, inspect raw responses, model stable endpoints, mutate config, compare behavior, and fuzz nearby request shapes without rewriting setup.
That matters because most security ideas are wrong. Good tooling kills wrong ideas faster.
The weekend produced:
| Finding | Status | Self-assessed score | High-level impact |
|---|---|---|---|
| Vulnerability 1 | reported, triage ongoing | 8.5 | 1-click account takeover on LAN |
| Vulnerability 2 | reported, triage ongoing | 8.7 | 1-click account takeover |
| Vulnerability 3 | still investigating | ? | got me unusually close to root privileges |
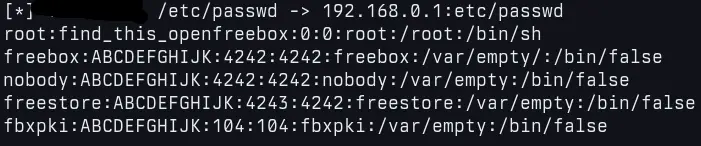
The third bug also made me rediscover an old Freebox easter egg. A Univers Freebox article tells the 13-year-old story around Doom, root access, 4242, and find_this_openfreebox: Après 13 ans, une faille insolite et ultra pratique sur une ancienne Freebox dévoilée mais….
Old consumer devices are funny because code survives.
 screenshot of me, reading
screenshot of me, reading /etc/passwd remotely, by exploiting my fancy third vulnerability
So, why the fuck did I write a Rust crate?
Because curl got me curious, Python got me moving, and then both became too annoying.
Because Freebox OS has enough surface area that the boring parts needed to be solid.
Because I wanted to learn Rust on something real.
And because after two private reports, one root-adjacent rabbit hole, and one decade-old easter egg, the crate became the only sane way to keep going.